Single Sign-On
Single sign-on (SSO) allows you to configure MAPS to use a common authentication server. There are two authentication methods supported: CAS authentication, and SAML 2.0 authentication. Single sign-on authentication can be used for eLauncher, Argos, and FormFusion. For security reasons, users are always prompted to log in when accessing IntelleCheck or MAPS Config.
There are two ways for users to log in when SSO is used:
- Users log in once to a central portal and then click a link to access the MAPS eLauncher.
- With a SAML server, users may also access the eLauncher from a browser, select the Single Sign-On button from the login dialog, and then enter credentials on a central SSO login page for authentication.
The single sign-on server handles the authentication, and provides a secure login to the MAPS launch page. If you already use single sign-on for other web pages, this can save time when accessing the products because users do not need to log in a second time.
Adding a CAS or SAML Server
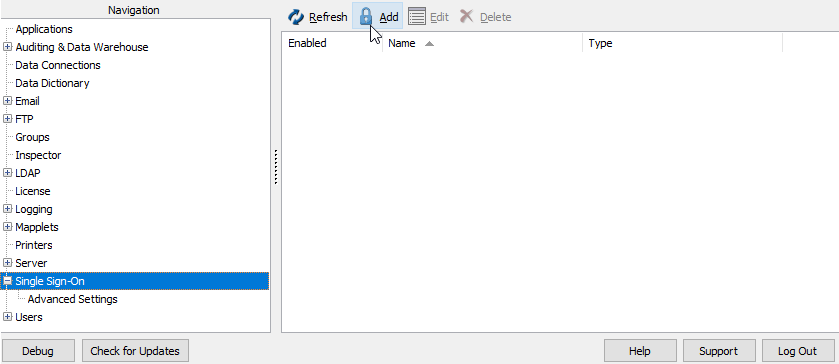
Select Single Sign-On from the Navigation pane. If one or more single sign-on servers have been added already, they will be listed here.
Click Add to display the Edit Single Sign-On Server configuration dialog.
Select the server type (SAML or CAS) from the Type menu.
The configuration dialog updates to show the configuration options for the type of server selected.
See CAS Servers or
MAPS allows you to configure any number of CAS and SAML servers, but you can have only one CAS and one SAML server enabled at a time. If multiple CAS servers are enabled, MAPS will use the first enabled CAS server in the list. If multiple SAML servers are enabled, MAPS will use the first enabled SAML server in the list. To disable a configured server, un-check the Enabled box for the server on that server's configuration dialog.
Advanced Settings
Under Advanced Settings a MAPS Administrator will have the option to enforce the use of Single Sign-On for all non-administrative users. If an exception is needed, a group can be added to an exceptions list to forgo this requirement.
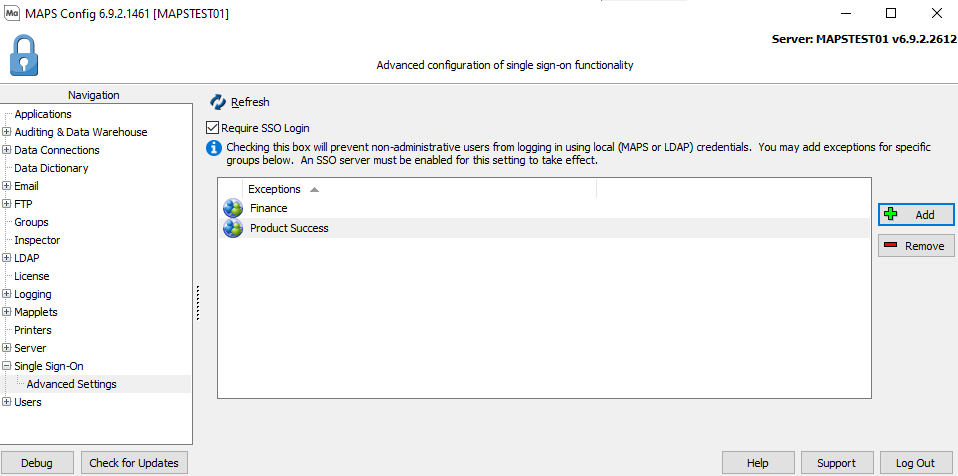
Require SSO Login: When checked by a MAPS Administrator, prevents non-administrative users from logging in to MAPS using local or LDAP credentials. For more information see the SAML Servers page.
Exceptions: This field shows the MAPS and/or LDAP groups that have been added to the exceptions list to allow for logging in without the use of Single Sign-On.
Add: This button adds a group to an exceptions list.
Remove: This button removes a group from an exceptions list.